Summary
This website contacted 8 IPs in 1 country across 10 domains to perform 1 HTTP transaction. The main domain is meine.santander.de.
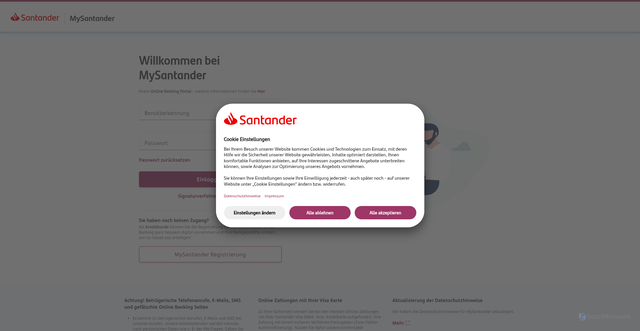
Submitted URL: https://sansign-login.app/
Effective URL: https://meine.santander.de/login/#/login/Redirected
AI Security Verdict
Confirmed Scam
Confidence: 95%
Phishing page impersonating Santander, new domain, harvests passwords – confirmed scam.
Risk Factors
Details
Bot Protection Detected
This website is protected by imperva bot protection. Our scanner was challenged or blocked during access.
Page Title
Login MySantander
Scan Type
public
Language
German
Category
finance banking
(59%)Domain Information
You're looking at domain 'sansign-login.app' on the application-focused generic top-level domain (.app). Its registrable label 'sansign-login' stretches across 13 characters split between four vowels and eight consonants, notching one hyphen. Splitting it apart reveals three words: san, sign, login. The median word length lands at four characters. No strong language cues emerged from the frequency lists.
Screenshot
Page Load Overview
Language Analysis
Primary Language
Detection Details
Website Classification
Primary Category
All Detected Categories
Detected Features
Domain & IP Information
| Requests | IP Address | Location | AS Autonomous System |
|---|---|---|---|
| 16 | 172.67.184.16 | United States | |
| 14 | 35.241.3.184 | Kansas City, Missouri, United States | AS396982Google LLC |
| 14 | 45.60.197.69 | United States | AS19551Incapsula Inc |
| 14 | 35.190.14.188 | United States | AS396982Google LLC |
| 14 | 91.235.133.67 | United States | AS30286ThreatMetrix Inc. |
| 14 | 91.235.134.131 | United States | AS30286ThreatMetrix Inc. |
| 14 | 192.0.78.27 | United States | Unknown |
| 14 | 91.235.132.130 | United States | AS30286ThreatMetrix Inc. |
| 114 | 8 | - | - |
Detected Technologies3
Content Similarity HashesFor malware variant detection
TLSH (Trend Micro Locality Sensitive Hash)
Security-focusedSpecialized for malware detection and similarity analysis
ssdeep (Context Triggered Piecewise Hashing)
Context-awareDetects similar content even with modifications
sdhash (Similarity Digest Hashing)
High-precisionHigh-precision similarity detection for forensic analysis
These hashes enable detection of similar websites and malware variants by comparing content similarity even when exact matches aren't found.
Image Hashes
Perceptual Hashes
Other Hashes
Scan History
Scan history not available
Unable to load historical scan data