Summary
This website contacted 2 IPs in 2 countries across 2 domains to perform 6 HTTP transactions. The main domain is recruit.ncl.res.in and was registered NaN years ago.
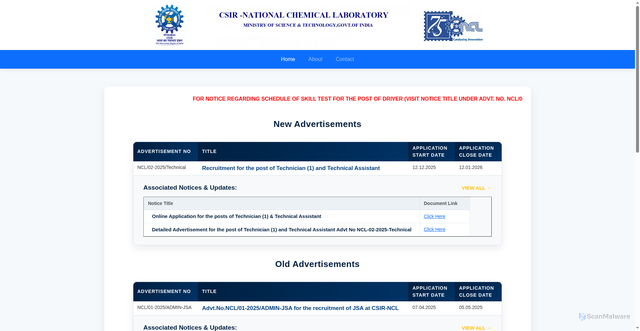
Submitted URL: https://recruit.ncl.res.in/
AI Security Verdict
Safe Website
Confidence: 95%
The site appears legitimate with no security concerns.
Safety Factors
Details
Page Title
Home Page - Recruit
Scan Type
public
Language
English
Category
documentation technical
(71%)Domain Information
Domain 'recruit.ncl.res.in' uses the Indian country-code top-level domain (.res.in), featuring subdomain 'recruit'. Count 3 characters in 'ncl' holding zero vowels versus three consonants. It segments into one word: ncl. Median word length is three characters. No strong language cues emerged from the frequency lists.
Screenshot
Page Load Overview
Language Analysis
Primary Language
Detection Details
Website Classification
Primary Category
All Detected Categories
Detected Features
Domain & IP Information
| Requests | IP Address | Location | AS Autonomous System |
|---|---|---|---|
| 3 | 151.101.193.229 | United States | AS54113FASTLY |
| 3 | 59.163.216.78 | India | AS4755TATA Communications formerly VSNL is Leading ISP |
| 6 | 2 | - | - |
Detected Technologies1
Content Similarity HashesFor malware variant detection
TLSH (Trend Micro Locality Sensitive Hash)
Security-focusedSpecialized for malware detection and similarity analysis
ssdeep (Context Triggered Piecewise Hashing)
Context-awareDetects similar content even with modifications
sdhash (Similarity Digest Hashing)
High-precisionHigh-precision similarity detection for forensic analysis
These hashes enable detection of similar websites and malware variants by comparing content similarity even when exact matches aren't found.
Image Hashes
Perceptual Hashes
Other Hashes
Scan History
Scan history not available
Unable to load historical scan data